Information Security at Georgia Tech
I began my foray into information security as an 11th grader when my AP CS teacher told me about a competition hosted by CMU called picoCTF. Interested and motivated (partially by a grade), I decided to compete in a team with two friends. I only completed one challenge by the end, but I fell in love with the process of learning. I learned about bitwise operations for the reversing challenges and watched hours of RSA lectures on YouTube to crack the crypto challenges. Of course, my understanding was still rudimentary at best (I concluded that I was supposed to just factor n with a brute force script for the RSA challenge - ha!). In the end, though, I couldn’t believe how much I had learned in such a short time about topics I didn’t even know existed. It was then that I decided to make computer security my career.
Going into Georgia Tech, I wasn’t sure what kind of infosec community would exist (if any at all). I was very fortunate to find that there was a club called GreyHat that had a huge following and passionate officers. Unfortunately, I was still a newbie and had little knowledge of computers in general. It was difficult to understand everything, but I regularly attended the CTF meetings where we solved challenges together. At the end of the year, I ran for and was elected CTF captain for the next year. I didn’t know much but I wanted to see the club succeed and to pass on whatever little knowledge I had.
CTF Club
Every Monday of my sophomore year, I’d fulfill my usual regimen of going to class, finishing homework, and (sometimes) hitting the gym. Around 7PM, after most people on campus had headed back to their dorms or the library, a group of passionate nerds and I would meet in an unused, cramped study space at the top floor of the CoC. Each week, I created a set of problems for the students to work through, each time teaching something new about the vast world of computers.
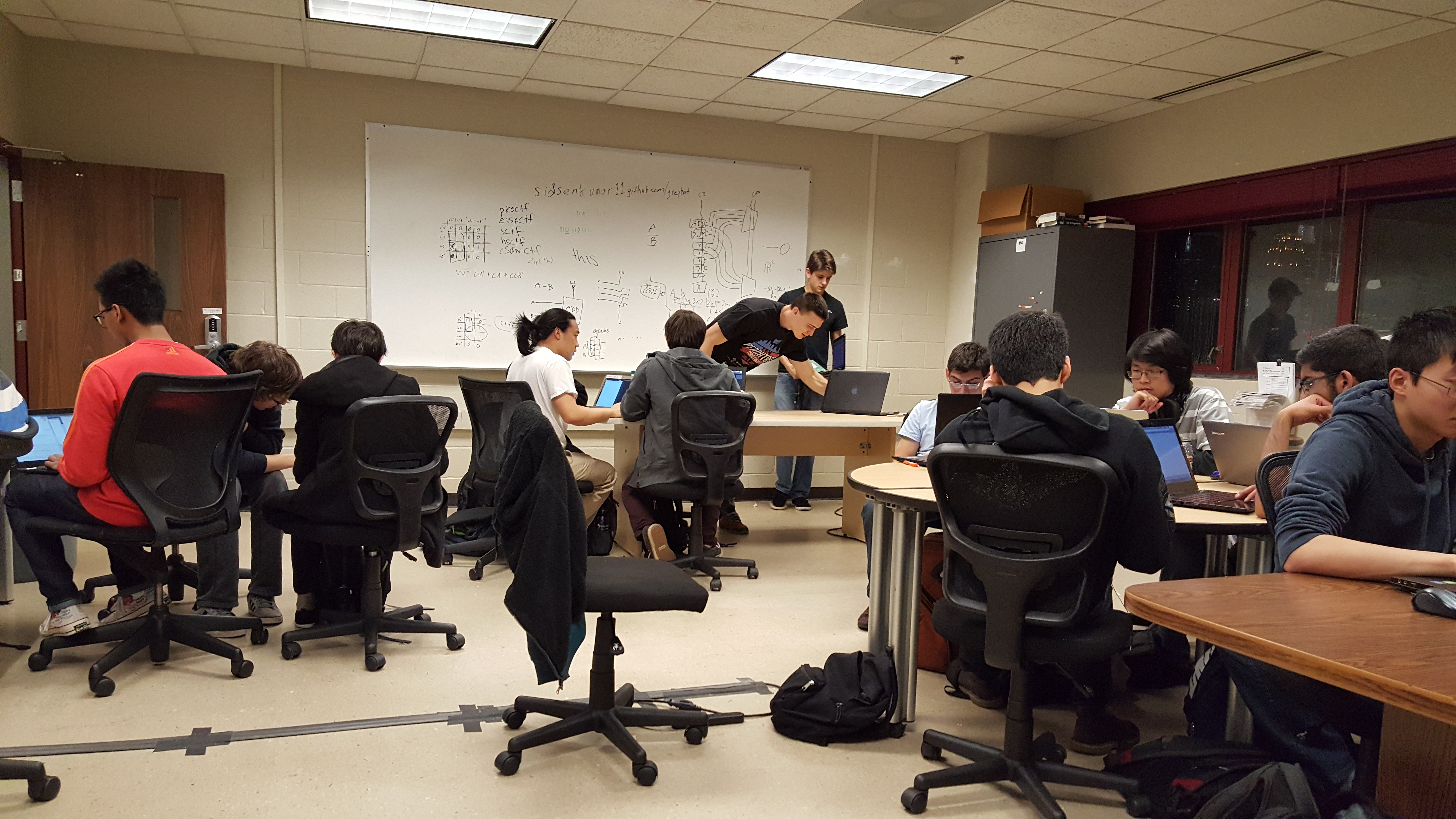
Of all the things I did in college, running CTF meetings was probably my favorite. I spent my time with an amazing group of people ranging from your typical computer science students to even mechanical engineers as they formed groups to tackle my problems. Later, many of them even became my close friends outside of GreyHat.
I can’t describe what an awesome feeling it was to see the relieved looks on everyone’s faces when they finally solved a problem after an hour of struggling through it. It was that same feeling that had led me to love computer security, and I was thrilled that I could pass it on to others.
CSAW CTF Experience
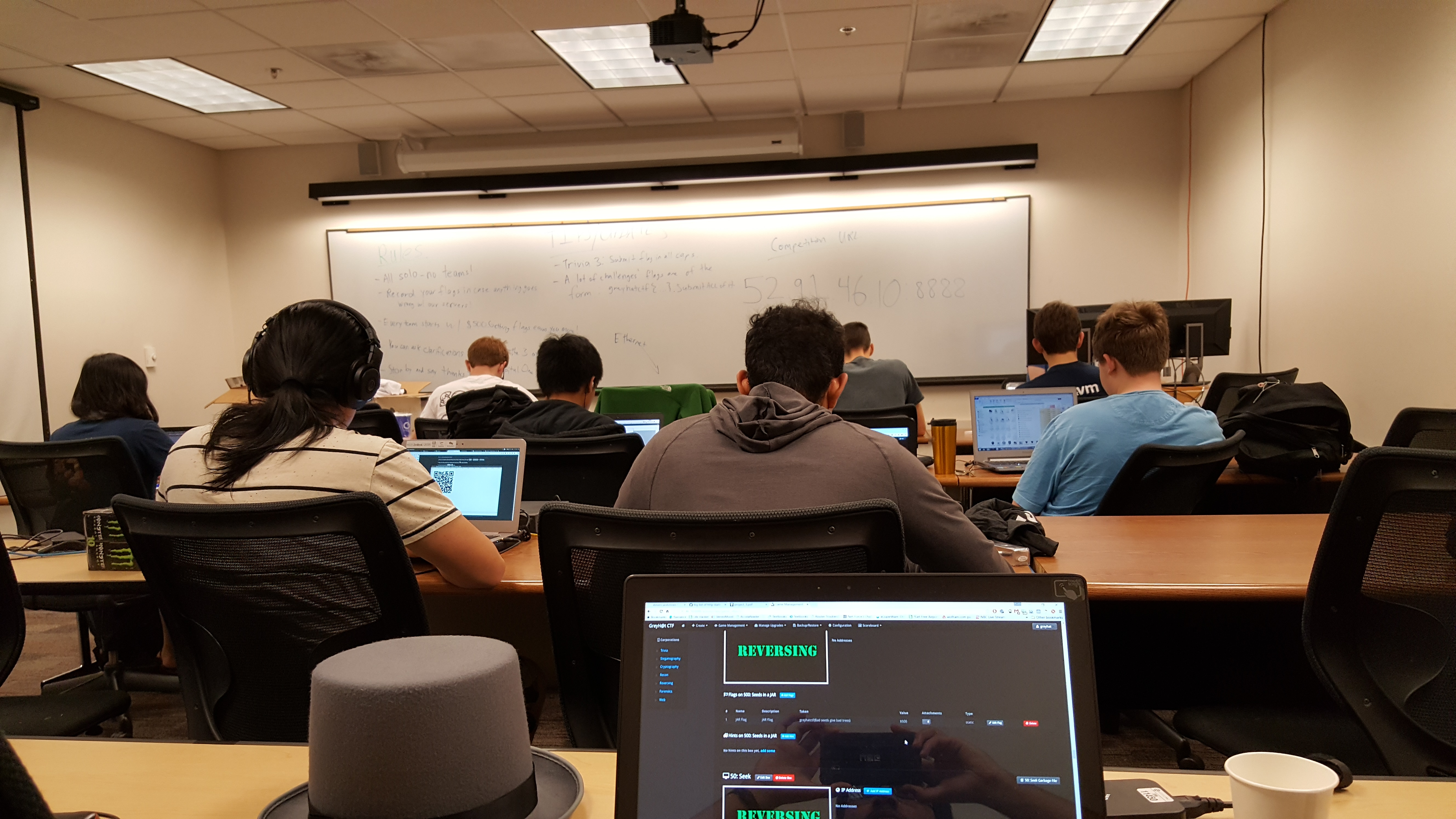
In the fall, we decided to compete online in the annual CSAW CTF Competition. We reserved our usual room, made pancakes and scrambled eggs to fuel us through, and called in some alumni (like the legendary Chris Grayson) for a whole weekend of hacking fun.
Somehow, by the end of the weekend, our Georgia Tech team ended up in 57th place out of 1367 teams in the competition. As it turned out, though, our team was 13th among the top 15 teams that qualified to go to the finals in New York City - so we did!

At CSAW finals, three others and I worked through a 36 hour non-stop hacking session on the problems we were given. While we jammed out to music and munched through an endless supply of free food for competitors, we solved many problems and learned many new things. I was still relatively inexperienced when I went, but I did manage to solve two challenges - a PDF forensics challenge worth 300 points and a simple file carving problem worth 50 points.
We didn’t win at the end of the competition but I did have one of the most fun hacking experiences of my life. It was an amazing feeling to be surrounded by so many intelligent people who shared the same passion as me. I highly recommend anyone interested in security at all to get their hands dirty with CTFs.
GreyH@t CTF
In the spring of 2016, GreyHat decided to revive its own annual CTF competition. We opened up the competition to undergraduate and masters students so that we could cater to a wide range of students without giving too much of an edge to higher level students.
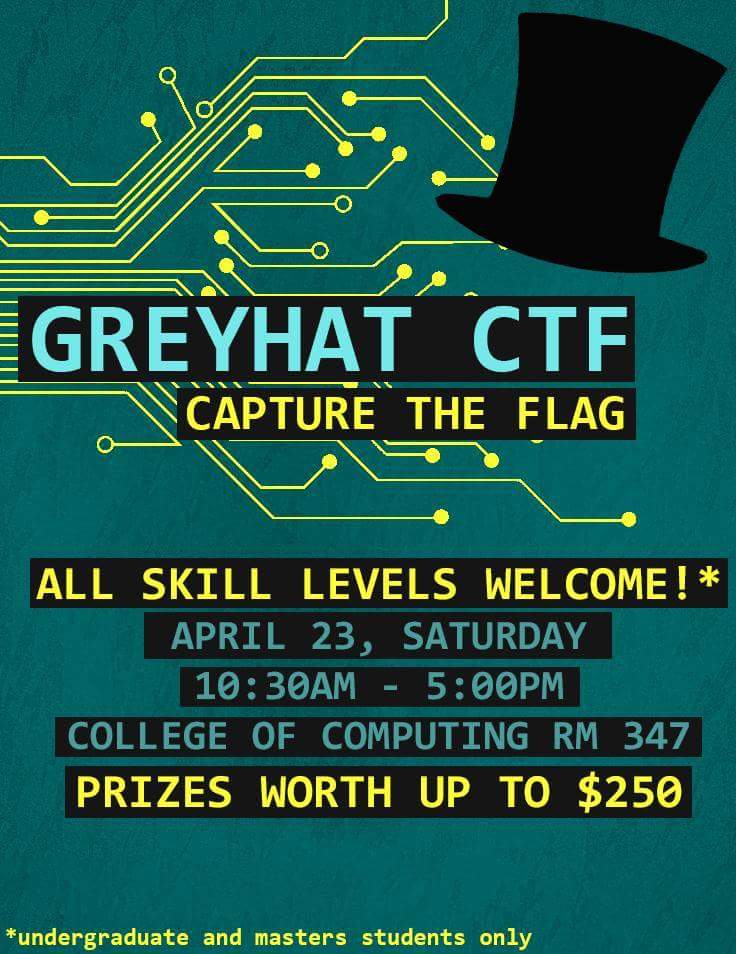
The competition received sponsorship from Capital One, which generously provided us with a $400 prize pool and even bought Moe’s catering. As members of GreyHat’s board, Manas George, Max Bires, and I authored a list of puzzles to be solved during the competition. We set up an instance of RootTheBox using AWS and let everyone work on the problems for nearly 8 hours.
Overall, it was a great success and everyone seemed to enjoy our CTF competition. You could visibly see the frustration on competitors’ faces as the competition was coming to a close and as they rushed to solve problems. It was a good kind of frustration; the kind that you learn from. I’m looking forward to doing something like this again in the future.
GreyHat Presidency
The following year, I was elected president of GreyHat. Being president meant that I was responsible for communicating with club members and faculty, organizing funding for club events, and most importantly, getting presentations for our regular meetings. I can honestly say that I was not prepared for the amount of work it was going to be - and I mostly blame my own lack of security knowledge. More than once I spent a weekend doing research on security topics I was unfamiliar with myself in order to give a presentation on it that week.
If I could have given myself one piece of advice, it would be to give more practice problems and fewer lectures. People really learn from doing problems together (something I had already figured out as CTF captain, duh!).
Despite my shortcomings, I really enjoyed getting to know the club members who were interested in what I taught and regularly came to my meetings. As I start my next chapter at UC Santa Barbara, I can only hope that the infosec community I meet will be as awesome and welcoming as the one I found at Georgia Tech.
Presentation Archive
Here is a list of all the presentations I’ve given for anyone that’s interested.
President Presentations
04-13-17: Elections and Password Hashing
02-02-17: Invisibility on the Web - Tor and VPNs (see here for YouTube Talk)
01-26-17: Remote Tutorial - Kali Linux Virtual Machine Setup
01-19-17: GreyHat Introduction 2
12-01-16: Web-App CTF Challenge
11-03-16: Padding Oracle Attacks
09-29-16: Forensics/Stego Problem (repeat of 11-16-15)
09-15-16: SQL Injection
09-01-16: GreyHat Introduction
04-07-16: Cross Site Scripting
CTF Captain Problems
My GreyH@t CTF 2016 Problems
11-16-15: CSAW’15 Forensics Problem
11-02-15: Crypto Practice Problems
10-05-15: Steganography
09-28-15: Practice Problems
09-21-15: Beginner Crypto
Presentations Not Given
One Time Pad
History of Cryptography
Bonus
Sometime in 2016, I had the pleasure of welcoming a security researcher from Booz Allen Hamilton named Dr. Malachi Jones to talk at GreyHat. Malachi also happened to be a graduate of Georgia Tech and ended up convincing me to work at Booz Allen for my next internship. I’ve included his presentation here as well because I thought it was really well put together and very informative.
Automating_Analysis_and_Exploitation_of_Embedded_Device_Firmware.pdf